Securing Australian Small Businesses!
Protect & Grow Your Business knowing your cyber security is covered!

Who Are We?
A Team of Cyber Security Experts Obsessed with Securing your Business.
We help private and public sector organisations of all sizes realise the opportunity of better cyber security in an increasingly complex and challenging threat environment.
Offering a set of services: consulting and advisory; Cybersecurity; security integration and engineering; Application Delivery Network; Application Security and Solutions; DevOps Subject Matter Experts and cyber security training.
How Can We Help You?
Cybersecurity
Cybersecurity is continually challenged by hackers, data loss, privacy, risk management and changing cybersecurity strategies. The number of cyberattacks is not expected to decrease in the near future. Moreover, increased entry points for attacks, such as with the arrival of the internet of things (IoT), increase the need to secure networks and devices.
- Identity and access management (IAM)
- Firewalls
- Endpoint protection
- Antimalware
- Intrusion prevention/detection systems (IPS/IDS)
- Data loss prevention (DLP)
- Endpoint detection and response
- Security information and event management (SIEM)
- Encryption tools
- Vulnerability scanners
- Virtual private networks (VPNs)
- Cloud workload protection platform (CWPP)
- Cloud access security broker (CASB)


Application Delivery Networking
Application security services are designed to protect critical business software from undesired access and mishandling, as well as viruses or other cyber attacks. Application security providers assist businesses with application security through steps including application design review, application code review, and secure application development
Application Security & Solutions
Application security services are designed to protect critical business software from undesired access and mishandling, as well as viruses or other cyber attacks. Application security providers assist businesses with application security through steps including application design review, application code review, and secure application development.



- Web Application Security
- SQL injection
- OWASP Top 10
- Cross site scripting (XSS) attacks
- DNS Spoofing
- Intrusion detection and intrusion prevention
Security Information and Event Management
- Real-time visibility across an organization’s information security systems.
- Event log management that consolidates data from numerous sources.
- A correlation of events gathered from different logs or security sources, using if-then rules that add intelligence to raw data.
DevOps Subject Matter Experts
DevOps Subject Matter Experts (SME) ensures the quality, reliability, and stability of all production systems and services while employing DevOps best practices. SMEs are cross-functional experts who are primarily charged with facilitating organizational collaboration, establishing and enforcing enterprise-wide processes and seeking opportunities for improvements in delivery.
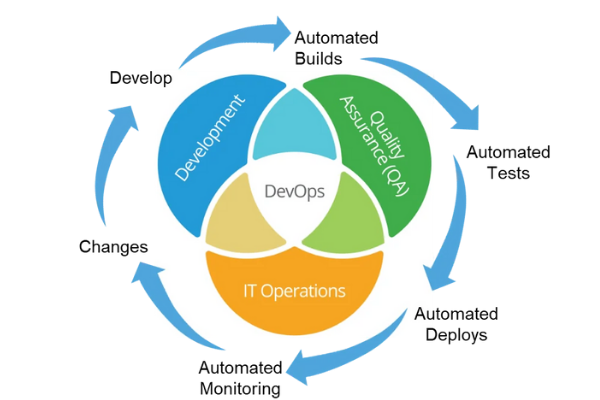

The Real DevSecOps Environment
- Security testing is done by the development team.
- Issues found during that testing is managed by the dev team.
- Fixing security issues stays within the dev team.
Calling all Graduates
- Calling all IT graduates
- Start your dynamic career in Network and cyber security
- We can only accept applications from Citizens or Permanent Residents of Australia or New Zealand.
Contact Us
Contact us or complete the form to learn how SecureInfo Solutions can help you achieve your cyber security goals.
Address
ABN 66602199486
52 Eastern Avenue, Panania NSW 2213
Australia
P: +61 405959851
E: 2213.manager@gmail.com
